Security Alert
This morning I received a notification from Amazon AWS that it was likely that the security on a client’s account had been breached. AWS robots had detected activity with the pattern of unauthorised access validated with high level security tokens. To their credit, Amazon included details of what had been observed along with suggestions of what to check and/or change as a result.
A quick review confirmed that there was something to be concerned about. Three new high level accounts had been created.
The accounts did not appear to have been used maliciously, but it was obvious that after deleting them, all of the valid passwords and access tokens had to be replaced. This is not overly difficult to do, and was completed quite quickly.
However, it was most likely that the environment of one of the (valid) users had been compromised and that advising them of their new access tokens (and passwords in some cases) was not as easy as sending a message or email!
How are new credentials shared securely?
NOT by email! Other than in very specialised circumstances, email is not at all secure. It is transmitted in plain sight and is generally stored (indefinitely) on multiple (insecure) devices and servers.
Sending passwords via text or SMS suffers the same problems as email. However, many of the IM platforms such as iMessage, Messenger, Telegram and others are somewhat more secure. This improvement arises since the actual transmitted messages are encrypted. Thus, the content is not exposed whilst in transit.
Even when transmission is secure, messaging a password is still not a good idea. Why? Because the messages are generally stored in plain text on the sender and receiver computers (or devices). Remember, in the current scenario we have to assume that there was a breach of security in the first place. This could easily have been unauthorised access to a user device.
Introducing SnapPass
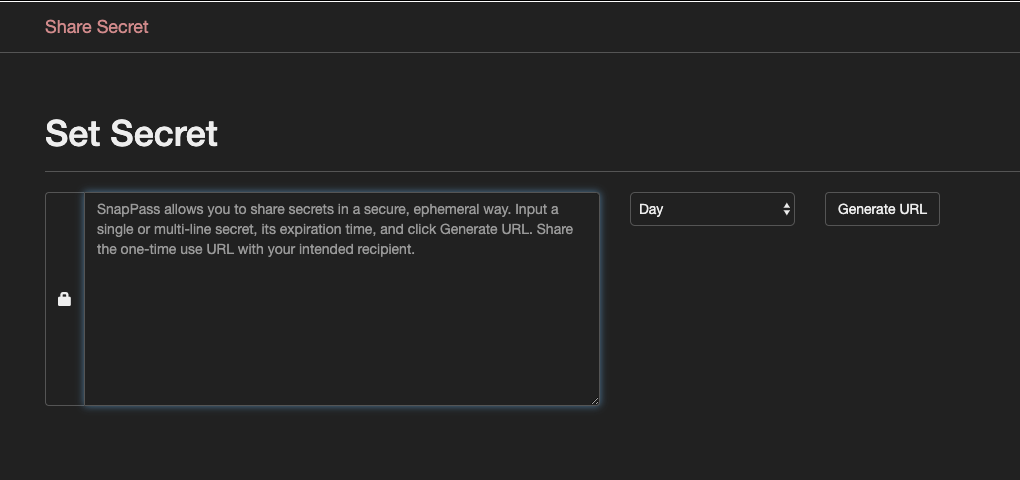
Sometimes called “snapchat for passwords”, SnapPass is a secure method of sharing passwords (or other secrets). SnapPass was developed by Pinterest and released as Open Source Software (OSS). Larger organisation can easily set up their own SnapPass service, the rest of us can use https://snappass.pw
SnapPass encrypts your secret and provides you with a time-limited secure URL which decrypts the secret (once) and then permanently deletes it. The secret itself is never logged or stored. You share the URL to provide one time access to your secret. If the recipient cannot see the secret before the URL expires, it means that your secret is no longer a secret!
Conclusion
So, why not bookmark https://snappass.pw so that next time you need to share a password or token protecting valuables, you can do so with well placed confidence.
A final word. Naturally, passwords should never be stored in plain text on any device. Doing so means that anyone with access to your device has access to all your secrets. Always use a reputable password vault such as 1Password to store passwords and other security tokens.